يحاول ذهب - حر
Six new security features Windows Server 2022 for Shielded
ADMIN #75: Teamwork
|ADMIN Network & Security
Configure the Secured-core server components to reduce the attack surface of your system with minimal overhead.

At first glance, Windows Server 2022 looks like a carefully modeled update of its direct ancestor, Windows Server 2019. Microsoft has clearly focused on evolution instead of revolution. However, a second glance reveals exciting new features, especially in the field of information security. Secured-core server sees Microsoft add no fewer than six components to its new operating system that boost the system’s security with minimal overhead. Whether an instance of Windows Server 2022 supports these features, and which ones, depends on the underlying hardware and whether you have a physical or virtual machine; the firmware and, in the case of a VM, the hypervisor, also need to be compatible.
Differences
Before I go into the details of and technical requirements for Securedcore server, I would like to prevent a misunderstanding. Microsoft also used the term “core” in connection with earlier editions of Windows Server, but that meant an installation without a graphical user interface. As early as Windows Server 2008 R2, you were allowed to choose between a core installation and a full installation with desktop display as part of the setup.
A Secured-core server and its functionality are different. You can use all of the new security features in conjunction with a graphical user interface in all editions. Windows Server 2022 Standard, Datacenter, and Datacenter Azure Edition support Secured-core servers, provided the hardware and virtualization are ready for them.
Secure Boot Explained
هذه القصة من طبعة ADMIN #75: Teamwork من ADMIN Network & Security.
اشترك في Magzter GOLD للوصول إلى آلاف القصص المتميزة المنسقة، وأكثر من 9000 مجلة وصحيفة.
هل أنت مشترك بالفعل؟ تسجيل الدخول
المزيد من القصص من ADMIN Network & Security

ADMIN Network & Security
Manage projects in SMEs with OpenProject Best-Laid Plans
OpenProject supplies sensible, comprehensive project management for SMEs with few financial inputs.
10 mins
ADMIN #75: Teamwork

ADMIN Network & Security
Synchronize passwords in KeePass Digital Safe
Usernames and passwords play an important role in security. In this article, we show you how to set up the KeePass password manager and keep it synchronized across multiple devices.
9 mins
ADMIN #75: Teamwork

ADMIN Network & Security
Test mechanisms for best practices in cloud design Best Clouds
Develop resilient and efficient cloud infrastructures for enterprise applications with the AWS Well-Architected Framework. We show you how to implement the solutions from the framework in practical terms by providing an introduction to the AWS Well-Architected tool with an example.
9 mins
ADMIN #75: Teamwork

ADMIN Network & Security
Six new security features Windows Server 2022 for Shielded
Configure the Secured-core server components to reduce the attack surface of your system with minimal overhead.
12 mins
ADMIN #75: Teamwork

ADMIN Network & Security
Cooperation with Cyn.in Fast Action
Cyn.in open source groupware focuses on connecting employees quickly and easily. We show you how to set up a Cyn.in environment, exchange knowledge, collaborate on projects, and manage processes. By Holger Reibold
7 mins
ADMIN #75: Teamwork

ADMIN Network & Security
Passkeys eliminate the need for password-based authentication Password Overboard!
Passwords are becoming a thing of the past. We look into the basic weaknesses of passwords, explain what passkeys are all about, and assess their practicality.
5 mins
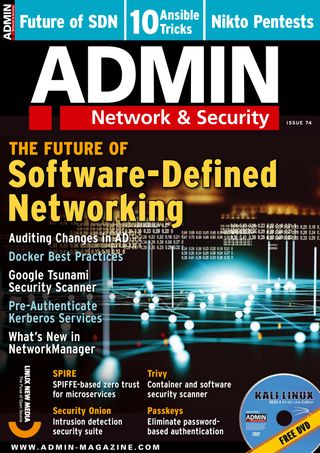
ADMIN #74: Software-Defined Networking

ADMIN Network & Security
Best practices when working with Docker images Shipshape
Whether you are developing containerized applications or running them, observing best practices helps to obtain optimal results.
7 mins
ADMIN #74: Software-Defined Networking
ADMIN Network & Security
Monitoring changes in Active Directory with built-in tools Tracking Down Attackers
Monitoring with built-in Windows tools can prevent the worst from happening after an attempted attack.
4 mins
ADMIN #74: Software-Defined Networking

ADMIN Network & Security
Discover vulnerabilities with Google Tsunami Before the Wave
Google Tsunami security scanner detects errors that typically signal danger and outputs alerts. We look into how you can get the tool up and running and even write the required plugins yourself.
10 mins
ADMIN #74: Software-Defined Networking

ADMIN Network & Security
Containers made simple Fully Automated
The Portainer graphical management interface makes it easy to deploy containers, relieving you of huge amounts of routine work you would normally have to handle with Docker, Podman, or Kubernetes. However, the licensing structure leaves something to be desired.
12 mins
ADMIN #74: Software-Defined Networking
Translate
Change font size